Top Security Awareness Training Programs for Employees
Understanding the Importance of Security Awareness Training
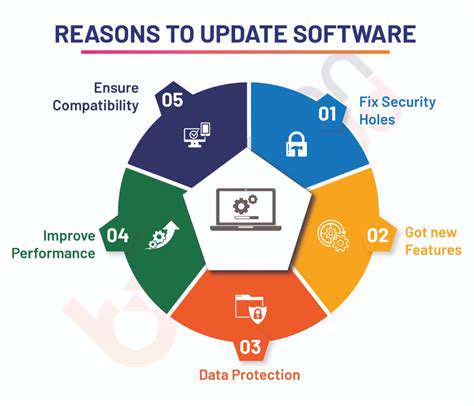
Security awareness training is crucial for any organization, large or small, to protect sensitive data and systems from potential threats. It equips employees with the knowledge and skills necessary to identify and report suspicious activities, ultimately reducing the risk of cyberattacks. Employees are often the first line of defense against security breaches, and a well-trained workforce is much more likely to recognize and avoid phishing attempts, malware downloads, and other malicious activities. This proactive approach to security is essential in today's digital landscape.
By fostering a culture of security awareness, organizations can significantly enhance their overall security posture. This proactive approach empowers employees to become active participants in safeguarding company assets, reducing the likelihood of costly data breaches and reputational damage. Security awareness training isn't just a one-time event; it's an ongoing process that should be integrated into the company's overall security strategy and reinforced regularly to maintain effectiveness.
Identifying the Key Elements of Effective Security Awareness Programs
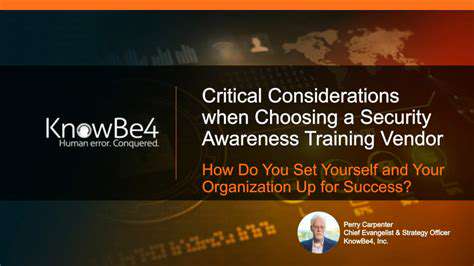
A truly effective security awareness program needs to go beyond basic information. It should incorporate interactive exercises, real-world scenarios, and regular reinforcement to ensure that employees retain the information and apply it in their daily work. This approach makes learning more engaging and memorable, increasing the likelihood of successful behavior change.
Key elements include clear and concise communication of security policies, regular updates on emerging threats, and opportunities for employees to ask questions and share concerns. This fosters a collaborative environment where employees feel empowered to report suspicious activities without fear of reprisal. Regular assessments and feedback are essential to ensure the effectiveness of the program and identify areas for improvement.
Tailoring Security Awareness to Specific Roles and Responsibilities
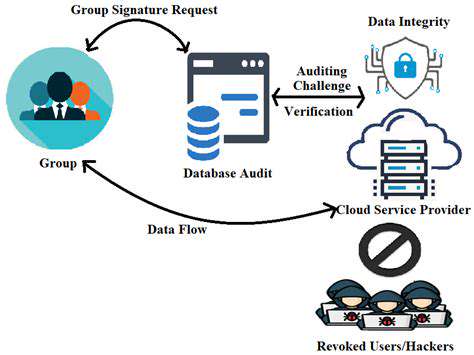
Organizations should tailor security awareness training to the specific roles and responsibilities of their employees. This targeted approach ensures that employees receive information relevant to their daily tasks and responsibilities, increasing the likelihood of successful knowledge retention and application. For example, employees handling sensitive data might need more in-depth training on data protection policies and procedures, while those who interact with external partners might need more information about phishing scams and social engineering tactics.
Different departments and teams within an organization may also have unique security needs. For instance, customer service representatives may require specialized training on handling sensitive information from clients, while IT staff might need more advanced training on system vulnerabilities and security protocols. By acknowledging these distinctions, companies can develop a more comprehensive and impactful security awareness program.
Measuring the Impact and Evaluating Program Effectiveness
Measuring the impact of security awareness training is crucial to ensure that the program is achieving its objectives. This involves tracking key metrics such as the number of employees participating in the training, the completion rate, and the improvement in employee knowledge and skills after the training. Regular assessments and surveys can also help identify areas where the program needs improvement or adjustment. By analyzing the results, organizations can refine their approach to better meet the evolving security needs of their employees.
Monitoring reporting rates of suspicious activities, analyzing user behavior after training, and assessing the reduction in security incidents are all valuable ways to evaluate the effectiveness of the program. By diligently tracking these metrics, organizations can demonstrate the value of their security awareness efforts and make informed decisions about future training initiatives.
Tailored Training for Specific Industries and Roles
Specialized Training for Healthcare
Healthcare organizations face unique security challenges, requiring tailored training to address specific risks like patient data privacy and HIPAA compliance. This specialized training should equip employees with the knowledge and skills to identify phishing attempts targeting sensitive patient information, understand the implications of unauthorized data access, and properly handle protected health information (PHI). Comprehensive training programs in this sector should cover various scenarios, from handling suspicious emails to recognizing potential security threats embedded within seemingly harmless documents.
Furthermore, regular updates on evolving threats and best practices are crucial. Healthcare professionals need to understand the ever-changing landscape of cyberattacks and the importance of adhering to strict protocols to maintain patient confidentiality and data security. This proactive approach to training will significantly strengthen the organization's overall security posture and mitigate potential vulnerabilities.
Custom Training for Financial Institutions
Financial institutions, handling sensitive financial data, need security awareness training programs specifically designed to address the high-risk nature of their operations. This training should focus on recognizing social engineering tactics, such as phishing attempts that target employees to gain access to accounts and sensitive information. Employees in these roles need to be equipped with the knowledge to identify and report suspicious activities, safeguarding their organization from potential financial losses and regulatory violations.
The training materials should also cover the importance of strong passwords, multi-factor authentication, and secure data handling procedures. This comprehensive approach empowers employees to act as the first line of defense against cyber threats and demonstrates a commitment to protecting sensitive financial information.
Tailored Training for IT Professionals
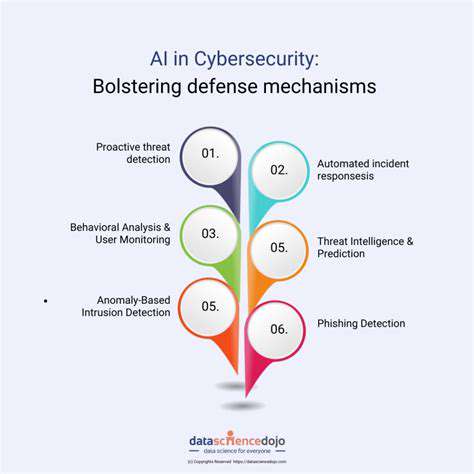
IT professionals require a different level of security awareness training compared to other employees. This training should focus on the technical aspects of cybersecurity, such as identifying malware, understanding network security protocols, and implementing appropriate security measures. They need to be equipped with the knowledge and skills to proactively identify and mitigate potential vulnerabilities within the organization's IT infrastructure.
It's essential for IT professionals to understand the latest security threats, attack vectors, and best practices for incident response. This specialized training should cover topics like secure coding practices, vulnerability management, and the importance of regular security audits. By empowering IT staff with this specialized knowledge, organizations can significantly reduce their risk exposure and improve their overall security posture.
Role-Based Security Awareness Training
Different roles within an organization have varying levels of access to sensitive data and systems. Therefore, security awareness training needs to be tailored to specific job functions and responsibilities. For example, customer service representatives require training on protecting customer data and recognizing suspicious requests, while executives need training on the risks associated with high-profile targets and the importance of board-level security protocols.
This role-based approach ensures that employees receive the most relevant and impactful training, allowing them to understand and address the security challenges specific to their daily tasks and responsibilities. By customizing the training based on each role, organizations can create a more comprehensive and effective security awareness program that enhances the overall security of the organization.
Measuring Program Effectiveness and Continuous Improvement
Defining Measurable Outcomes
A crucial first step in measuring program effectiveness is defining specific, measurable, achievable, relevant, and time-bound (SMART) outcomes. Instead of simply stating that you want to improve security awareness, pinpoint what constitutes a demonstrable improvement. This might involve reducing phishing click-through rates by 15% within the next quarter or achieving a 10% increase in user identification of malicious links in simulated phishing emails. Clearly outlining these goals allows for accurate tracking and evaluation of progress.
These measurable outcomes should be directly tied to the overall security objectives of the organization. For example, if a key objective is to reduce data breaches, then the outcomes should reflect actions to prevent data breaches such as increased user recognition of social engineering tactics or improved reporting of suspicious emails. Linking program outcomes to organizational goals provides a clear context for the effectiveness of the security awareness training.
Implementing and Tracking Key Metrics
Once you've established measurable outcomes, you need a system for consistently tracking progress. This often involves implementing key performance indicators (KPIs). Examples of KPIs for security awareness programs include phishing simulation click-through rates, user participation in training modules, and the number of reported security incidents. Regular reporting on these metrics is essential for identifying areas of success and areas requiring improvement.
Implementing a robust reporting mechanism is vital. This could involve using dedicated security awareness training software that provides detailed analytics or creating a simple spreadsheet to track key metrics. The key is to ensure that data is collected and analyzed regularly, ideally on a weekly or monthly basis, to identify trends and patterns.
Analyzing Results and Identifying Gaps
Regularly reviewing the collected data is crucial for understanding the effectiveness of the program. Identify trends, patterns, and areas where the program is not achieving the desired outcomes. For instance, if the click-through rate on phishing simulations remains consistently high, it might indicate a need for more targeted training or a different approach to communication about security threats.
Don't just focus on the negative; also highlight successes. Recognizing and celebrating improvements in user behavior or reporting rates can reinforce positive security habits and motivate continued participation in the program. This data-driven analysis allows for a proactive approach to continuous improvement, rather than reacting to problems after they've occurred.
Utilizing Feedback Mechanisms
Collecting feedback from program participants is essential for understanding their experience and identifying areas for improvement. This can be achieved through surveys, feedback forms, or even informal discussions during training sessions. Understanding user perspectives can help tailor training content, delivery methods, and communication strategies for better engagement and comprehension.
Continuous Improvement Strategies
Based on the analysis of results and feedback, develop strategies for continuous improvement. This could involve adjusting training materials, refining communication channels, or implementing new training modules to address specific knowledge gaps. It is important to be adaptable and responsive to the changing security landscape. New threats and vulnerabilities emerge constantly, so the security awareness program should be flexible enough to incorporate new information and adapt to changing circumstances.
Regularly reviewing and updating the program based on the collected data ensures that the security awareness training program remains relevant and effective in mitigating security risks. Continuous improvement is a key component of a successful and impactful security awareness program.
Read more about Top Security Awareness Training Programs for Employees
Hot Recommendations
- Review: The New [Specific Brand] Smart Lock Is It Secure?
- Best Budget Studio Monitors for Music Production
- Top Flight Simulation Peripherals (Joysticks, Throttles, etc.)
- Top Portable Scanners for Document Management On the Go
- Reviewing the Latest Smart Air Purifiers for Your Home
- Best Portable Photo Printers for Travelers and Memory Keepers
- The Future of Personal Transportation Beyond Cars (Hyperloop, eVTOL)
- Top Network Monitoring Tools [Free & Paid Options]
- Understanding the Tech Behind mRNA Vaccines [A Look Inside]
- Guide to Choosing the Right Gaming Chair for Ergonomics





![The Impact of Quantum Computing on Security [Future Threats]](/static/images/25/2025-06/DevelopingQuantum-ResistantCryptography3AANecessaryResponse.jpg)
![Best Gaming PCs You Can Buy Right Now [2025]](/static/images/25/2025-06/KeyComponentsDriving2025Performance.jpg)